Rowhammer Revisited: From Exploration to Exploitation and Mitigation
Abstract
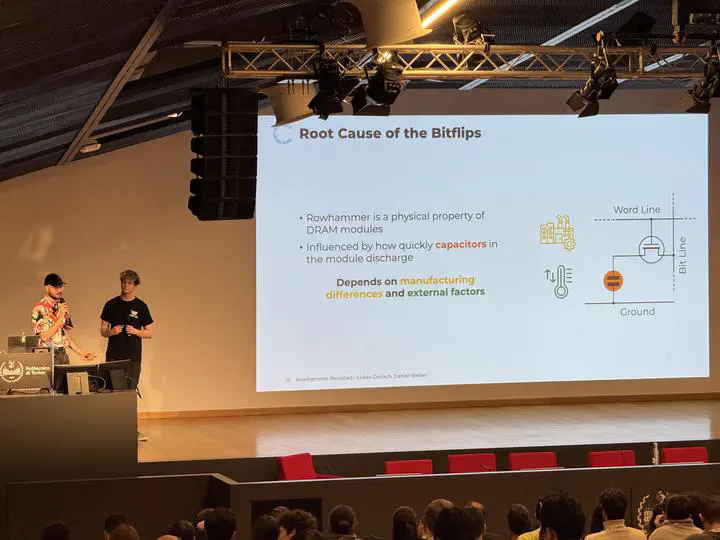
Rowhammer has been a busy field in system security research since its discovery in 2014. Until the current day, it remains the most prevalent fault injection attack on modern computing platforms. In this talk, we explore Rowhammer in three chapters: Exploration: Our first part investigates the intricate process of reliably triggering Rowhammer bitflips. We explore manual and fuzzing-based techniques that maximize the number of bitflips for different DRAM architectures. In addition, we present our most recent research on the transferability of bitflips and the evaluation of Rowhammer fuzzers. Exploitation: The second part of our presentation shows a broad range of Rowhammer exploitation techniques. We analyze existing exploits on various targets ranging from virtual machines to cryptographic algorithms to neural networks, demonstrating the capabilities and limitations of Rowhammer as an attack vector. Our talk discusses rapid prototyping techniques for crafting novel exploits and even introduces the concept of simulating Rowhammer exploits as presented by our research. Fixing Rowhammer: Finally, we give an overview of solutions that mitigate the Rowhammer vulnerability. We discuss proposed and implemented solutions on both the hardware and software levels, examining the effectiveness of various mitigation techniques. We evaluate the trade-offs and challenges of mitigating Rowhammer and discuss the ongoing efforts to secure systems against this threat.